TL;DR
.BGI files can be sent on mail as attachment and can execute code when opened.Requires that BGinfo.exe has been run on the remote machine once. It will also bypass Outlook attachment protection (Fixed with Defense-in-depth patch from September 2017). PowerShell functions to generate BGI and VBSWebMeter here: https://github.com/api0cradle/BGInfo
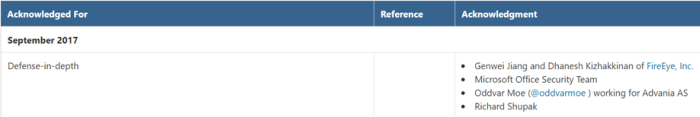
I was acknowledged on the MSRC acknowledgments page and I wanted to do a quick little write-up on my contribution to the Defense-in-depth patch.
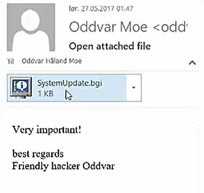
Earlier this year I discovered that you can use BGInfo to execute code to bypass application whitelisting with the use of .BGI files. After this blogpost I also discovered that .BGI files are in fact not blocked by Microsoft Outlook as an attachment (I guess you see where this is going). It turned out if BGinfo had been executed one time on a computer it would associate .BGI files with BGinfo (nice). So I tried to send myself a .BGI file and open the attachment. “boom”, it executed beautifully.
At first I was really excited since Microsoft offered bounty for similar types of attacks.
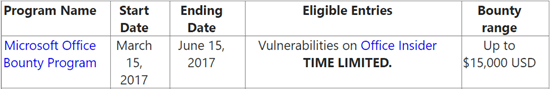
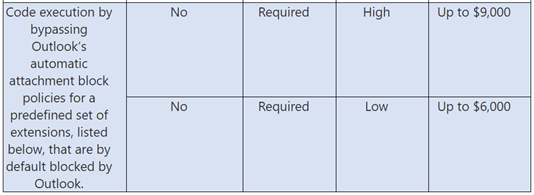
The problem with this was that .BGI files was not a part of the predefined list that would trigger a bounty (bummer). Money is not something that drives me, but it would be a nice bonus to have.
The list of extensions that would have qualified for a bounty: ade;adp;app;asp;bas;bat;cer;chm;cmd;cnt;com;cpl;crt;csh;der;diagcab;exe;
fxp;gadget;grp;hlp;hpj;hta;inf;ins;isp;its;jar;jnlp;js;jse;ksh;lnk;mad;maf;mag;
mam;maq;mar;mas;mat;mau;mav;maw;mcf;mda;mdb;mde;mdt;mdw;mdz;
msc;msh;msh1;msh2;msh1xml;msh2xml;mshxml;msi;msp;mst;ops;osd;
pcd;pif;pl;plg;prf;prg;ps1;ps2;ps1xml;ps2xml;psc1;psc2;pst;reg;scf;scr;sct;
shb;shs;tmp;url;vb;vbe;vbp;vbs;vsmacros;vsw;ws;wsc;wsf;wsh;xbap;xll;xnk
I also created two PowerShell functions to create this BGI file and the needed VBS script. More on this here: https://github.com/api0cradle/BGInfo
This is how a typical mail would look like.
A video where I used an earlier version of my script to demonstrate the PoC for Microsoft. (no music – sorry)
This issue is fixed with the Defense-in-depth patches for September 2017. I have verified on Office 2016.
Office 2016: https://support.microsoft.com/en-ca/help/4011126/descriptionofthesecurityupdateforoffice2016september12-2017
Office 2013: https://support.microsoft.com/en-au/help/4011103/descriptionofthesecurityupdateforoffice2013september12-2017
Office 2010: https://support.microsoft.com/en-us/help/4011055/descriptionofthesecurityupdateforoffice2010september12-2017
Office 2007: https://support.microsoft.com/ms-my/help/4011063/descriptionofthesecurityupdatefor2007microsoftofficesuiteseptember12-2
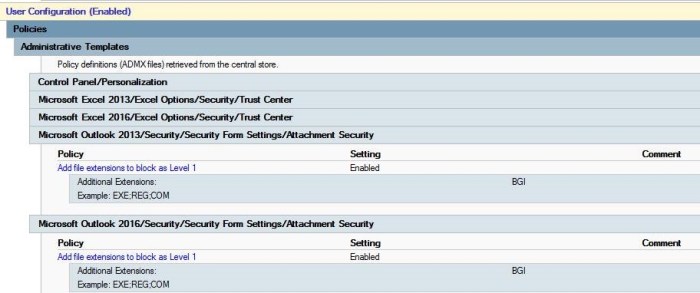
If for some reason you are not able to patch and need to fix this at once I recommend that you implement blocking of .BGI files. This can be done by adding block rule in Group Policy like this:
Hope you liked my write-up, and as always feedback is mostly welcome.
Disclosure timeline:
05/26/2017: Report submitted to secure@microsoft.com
06/02/2017: Response from Microsoft that it was sent to Product team.
06/16/2017: Response from Microsoft that it was not bounty worthy due to the list of predefined files.
08/01/2017: Confirmation that it will be fixed in the Defense-in-depth patch of September 2017
09/12/2017: Patch released
One thought on “Defense-In-Depth write-up”